Which Systems Would You Want to Engage to Support This Family? Social Work
Did yous know that, on boilerplate, 6 billion SMS messages are sent every day in the U.S. lone? That's 180 billion each month and 2.27 trillion each twelvemonth. Globally, four.ii billion people are texting worldwide. No doubt you're ane of 'em—which means yous fire off approximately 67 texts a day. That's a lot of "LOL"s.
When you transport all those texts, you probably presume that you lot and your recipients are the but ones privy to the information contained within. That's where you'd exist incorrect.
The truth is that text letters aren't secure, and that insecurity opens y'all, your friends, family unit, and business up to take a chance. And it isn't even your error; the default text messaging services many of u.s.a. use are old and vulnerable to a number of different set on scenarios. While carriers are on a path to update information technology, it might be besides piffling, too late.
Simply before you tin understand why you should spend more than energy on practicing safe texting, it may be helpful to understand how the whole system works in the kickoff place. Hither'due south the breakdown.
What Is SMS?
If you lot're sending a text bulletin, y'all're generally sending an "SMS," which stands for Short Bulletin Service. It'southward the oldest and i of the most widely used text messaging services today. Information technology includes MMS (Multimedia Messaging Service) which enables SMS users to send multimedia content like images, audio, and visual files. Both SMS and MMS are sent using cellular networks and thus require a wireless plan and a wireless carrier.
If you ship a traditional "text" message on your phone, it's considered an SMS. When y'all send that gif, you've just sent a MMS.
How Does SMS Work?
When you send a text bulletin, it first goes to a nearby cellular belfry over a pathway called the control channel, and and so into an SMS center (SMSC). The SMSC resends that message to the belfry closest to the recipient, and then it goes to their phone. SMS also sends data associated with the message, including the length of the message, format, time stamp, and destination.
Of the 109 text letters I sent yesterday, for example, 15 of them were SMS messages sent to people who accept phones on other carriers, seventy were sent through iMessage, and the rest were sent via OTT applications.
What Are OTT Applications?
WhatsApp, iMessage, Facebook Messenger, WeChat, and other messaging apps are grouped together every bit OTT applications and are also considered texting services. OTT stands for "Over the Top"; equally a group, these apps are different than SMS services because they apply cyberspace protocols (IP) rather than cellular networks to transmit messages. This ways these messages are sent through an cyberspace connection (aka WiFi) or via mobile internet connectedness.
How Do OTT Applications Work?
OTT apps work in a way that's different than SMS considering they transport encrypted messages that only you and the person receiving your bulletin can access. That means the messaging service doesn't know what y'all're sending, and neither does anyone else who might intercept that web traffic.
For example, WeChat uses extensible Messaging and Presence Protocol (XMPP) to commutation information between the users. This protocol is decentralized, and as a result, considered secure and flexible. The company as well uses SSL/TSL encryption. All of this is intended to ensure that other people aren't seeing your messages.
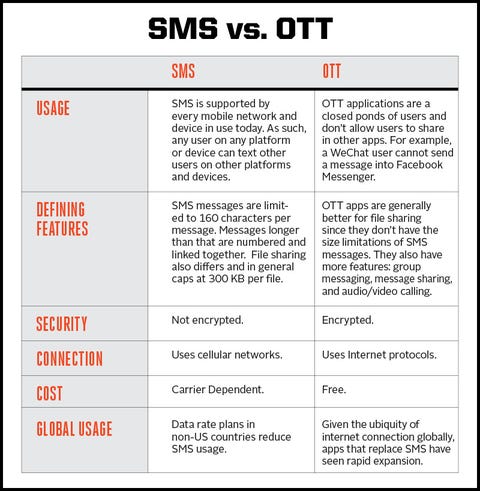
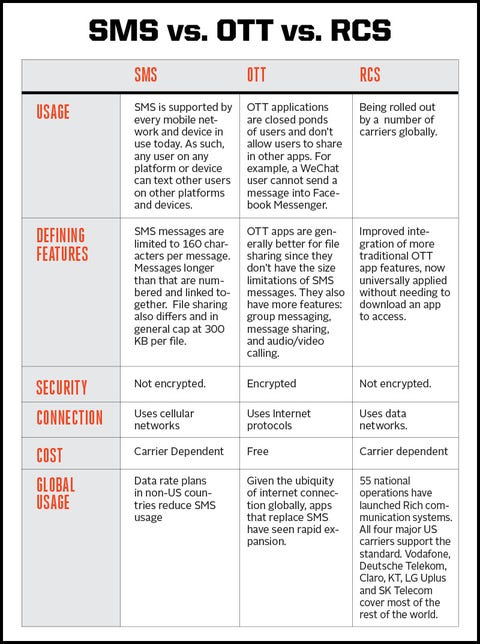
The Pros and Cons of SMS vs. OTT
When because messaging services, people ofttimes have to choose between sending via SMS or sending via an OTT service. If yous've traveled extensively outside the U.S., you lot've probably noticed that people in many other countries adopt WhatsApp to text messaging.
SMS is the almost ubiquitous, but to the lowest degree secure messaging medium. OTT apps require you to be using the aforementioned platform as the person you're messaging, which can be annoying. Perchance your friends don't want to download another app merely for texting, but standing to utilise SMS could put you at gamble because it doesn't have terminate-to-stop encryption.
The Side by side Evolution: Rich Communication Services (RCS)
Equally OTT apps cannibalize the SMS market, carriers take become incentivized to better SMS services in the form of Rich Advice Services (RCS). RCS theoretically combines the best features of OTT apps into one protocol that's universal beyond carriers and devices. This new protocol volition replace SMS and has been a piece of work in progress for more a decade.
Canonical by the GSMA in 2008, RCS was fully adopted in 2016. Since then, the RCS Universal Profile has been pushed out with strong support and dorsum-end services from Google (which caused Jibe) with the goal of providing consistent interoperable messaging services across all devices and networks. This not only helps create a global standard, but as well improves Android capacity, which is notoriously more than vulnerable to attacks. As Dan Wood of Bishop Fox noted in an interview, "A lot of SMS phishing is done confronting Android platforms."
RCS has the power to:
- Integrate with contact apps to come across who supports the service.
- Create group chats.
- Transport video and sound letters.
- Send howdy-resolution images upwards to x MB in size .
- Share location.
- Receive read receipts.
- See when people are replying in existent time.
- Default to SMS or MMS when the recipient doesn't support RCS.
- Meet live updates virtually upcoming trips and boarding passes.
Notwithstanding, while RCS doesn't accept cease-to-end encryption, it does have the standard security protocols of Transport Layer Security and IPsec.
RCS doesn't use cellular connection, but instead relies on a data connection and is both hardware- and platform-agnostic. Sprint, US Cellular, and Google Fi have implemented RCS fully across their networks and all devices. Other networks are implementing information technology against specific devices with broader plans to roll out farther through 2020. And, moving forrard, all devices should support this feature out of the box.
In short, RCS is an try by carriers to ensure the continued use of out-of- the-box messaging services and the continued data plans that accompany such usage. Withal, it doesn't enhance the overall security of information shared.
Why Should I Care If My Texts Are Secure?
With the recent ghost texting controversy, people have started to question just how secure text messages are. The uncomplicated answer: not very.
Remember: Text messages are sent in a multi-step process. While your message might be encrypted from your phone to the first jail cell belfry, it'south non encrypted later on that. And your SMSC may keep the message even if both the sender and recipient delete it. Whenever a message is encrypted, it tin be read by the mobile service, hackers, or governments.
"Because of the lack of encryption, hackers can search for weak points anywhere along the virtual path between the sender and receiver, which includes a ton of different network devices and calculating systems at many different providers—only 1 of which needs to exist exploited via technical vulnerability, misconfiguration, social engineering or insider attack," says Christopher Howell, CTO of Wickr.
"Considering the messages are stored on these systems longer than necessary," Howell continues, "it increases the window of vulnerability through which the hacker tin attack. Rather than having to defend a system for a few seconds to prevent a hacker from stealing a message, it needs to exist protected for days, weeks, months. These odds favor the hacker."
It'due south unlikely that you're using your cell phone to text about military launch codes, top hugger-mugger government business, or anything else that's of much use to the average hacker. Just what about a text exchange well-nigh a friend's decision to exit their spouse, your boss'southward cancer scare, or your petty sister's decision to switch jobs? Would you want that information to get disseminated somewhere else? What about data about your children, your pets, or a naked selfie that could help someone track where you lot are, guess your passwords, or find the tattoo on your left thigh that'due south also your banking concern account password?
It'south not always well-nigh protecting large secrets—it's about ensuring personal privacy for everyone involved.
Why Should I Care About SMS Security In General?
In that location are a number of means that malicious actors (governments, terrorists, etc.) can hack into SMS systems and utilize them for their ain do good.
Governments are hacking using SMS. Chinese hackers recently did this when they developed malware to steal SMS messages. The malware used a keyword list of terms that were of geopolitical interest for Chinese intelligence drove and and then connected those terms with telephone numbers that they and so tracked. The group responsible for this (APT41) too interacted with call detail records and tracked high-ranking individuals who were of involvement to Chinese intelligence.
"At that place are '0day' bugs on the market place that tin can remote access your telephone without you having to click on any sort of link or do anything at all," says Ben Lamm, the CEO of Hypergiant. "In fact, this market is growing as are all threats to vulnerable systems. The hush-hush here is that we need to all be more focused on security, on protecting ourselves from vulnerability and on understanding that ane insecure private can compromise the whole group."
Take, for instance, 2-factor authentication, which we more often than not think of as safe. If that second factor hallmark is through an SMS service, it could be intercepted, meaning the system you thought was secure might at present be compromised. This is important if, say, y'all employ two-factor authentication to protect your bank account, corporate email, or dating contour.
Regular people are hacking and being hacked using SMS, too. "Text message hacks are happening everywhere, from middle schoolers hacking their enemies to steal their pictures to nation country level attacks," says Georgia Weidman, the founder of Shevirah Inc. and a New America Cybersecurity Policy Fellow.
What Apps Offer End-to-End Encryption?
Given the propensity for and variety of attacks, it makes sense to consider alternative services that offer cease-to-finish encryption. Popular secure apps include:
- Apple'south FaceTime
- Apple's iMessages
- Signal
- Wickr
- Wire
"An attacker might send a text message enticing a user to log into their bank or download a malicious application. Many users are getting security awareness training to be wary of phishing via email, but that didactics is often lacking around mobile based attack vectors such as text message or WhatsApp," Weidman says. "Additionally, the text messaging programs on our phones are simply software similar any other and thus prone to security vulnerabilities. There accept been instances in the by where an attacker could send a malformed text message to a device and proceeds control of the device."
The truth is we all need to utilize an actress dose of mutual sense.
"Employ the same caution when responding to SMS text letters equally you would a suspicious email," says Kristin Kozinski of Don't Click on That. "When evaluating a message consider the source of the message. If y'all don't recognize the number, confirm the context of the message elsewhere. For example, if your banking concern texts you, call the customer support number to verify the message you received. Be cautious of any link in the text bulletin. This is a prime outlet for distributing malicious URLs. Finally, if the text sounds too good to be truthful, it probably is."
This content is created and maintained past a tertiary party, and imported onto this page to help users provide their email addresses. You may be able to detect more than information well-nigh this and similar content at pianoforte.io
Source: https://www.popularmechanics.com/technology/security/a29789903/what-is-sms/
0 Response to "Which Systems Would You Want to Engage to Support This Family? Social Work"
Post a Comment